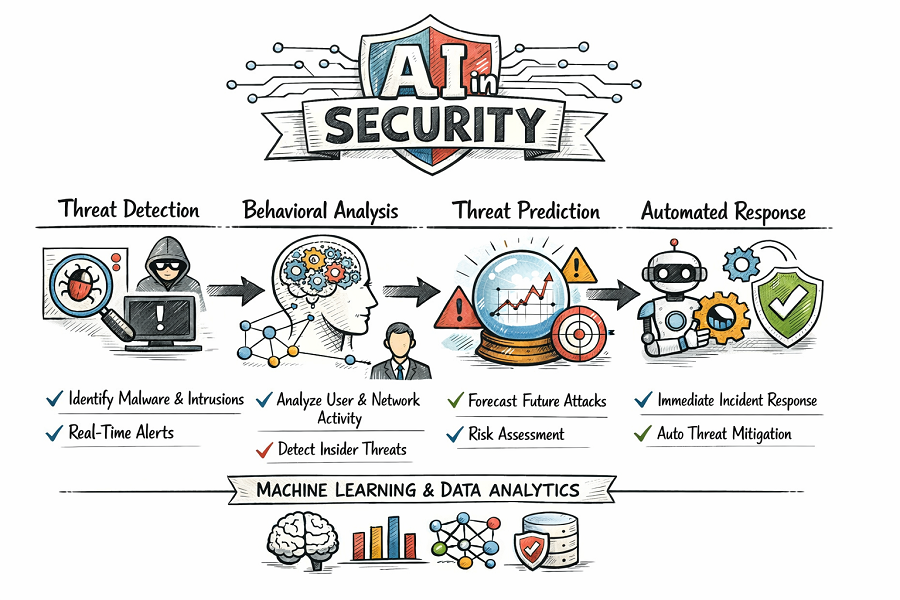
In today's hyper-connected and threat-laden digital environment, relying on a patchwork of disconnected, siloed security tools is a recipe for disaster. This has led to the rise of the integrated AI in Security Market Platform, a strategic shift towards a unified and holistic security architecture. This platform is not a single product but an integrated ecosystem that serves as a central nervous system for an organization's defenses. Its primary purpose is to ingest, aggregate, and normalize vast streams of data from every corner of the digital estate. This includes logs from endpoints (laptops, servers), network traffic data, alerts from email gateways, user authentication events from identity systems, configuration data from cloud environments, and even feeds from physical security systems like video cameras and access card readers. At its heart, this platform is a massive data lake combined with a powerful AI and analytics engine. By centralizing all security-relevant data, the platform's AI can correlate seemingly unrelated events to uncover complex, low-and-slow attack campaigns that would be completely invisible to individual point solutions, providing a single, coherent view of the organization's security posture.
A prime example of this platform-centric approach in action is the paradigm of Extended Detection and Response (XDR). XDR represents a significant evolution from its predecessor, Endpoint Detection and Response (EDR), by extending its visibility and control beyond the endpoint. The "X" in XDR stands for "extended," signifying its ability to collect and correlate data from a much broader set of sources, including network infrastructure, cloud workloads, and email systems. The true power of an XDR platform lies in its embedded AI engine. When an attack occurs, it rarely touches just one system. An attacker might start with a phishing email, gain a foothold on an endpoint, and then move laterally across the network to access a cloud server. An XDR platform's AI can automatically stitch this chain of events together, connecting the dots between a suspicious email, an unusual process execution on a laptop, and an anomalous API call in the cloud. It then presents this entire attack storyline to the analyst in a single, visualized incident report, transforming a flood of disparate alerts into a clear, actionable narrative and dramatically reducing investigation and response times.
The modern AI security platform is often built upon the foundational technologies of Security Information and Event Management (SIEM) and Security Orchestration, Automation, and Response (SOAR). Traditionally, SIEMs were passive log repositories that relied on rigid, human-written correlation rules. Today's next-generation SIEMs are infused with AI, most notably through User and Entity Behavior Analytics (UEBA). UEBA uses machine learning to build a dynamic baseline of normal behavior for every user and device on the network and then detects risky anomalies. SOAR platforms take this a step further by automating the reaction to these AI-driven detections. A SOAR platform acts as the "hands" of the security operations center, integrating with all other security tools. When a credible threat is identified, the SOAR platform can automatically execute a pre-defined "playbook" of response actions, such as isolating an infected machine from the network, disabling a compromised user account, or blocking a malicious IP address at the firewall, all without requiring any human intervention and enabling response at machine speed.
The ultimate vision and logical endpoint for the AI in security platform is the creation of a truly autonomous, self-defending digital ecosystem. This futuristic concept, often referred to as a "Security Autonomic Nervous System," draws an analogy to the human body's immune system. In this model, the AI platform would not only detect and respond to threats but would also predict them and proactively adapt the environment to prevent them. It would continuously monitor the global threat landscape, analyze its own network's vulnerabilities, and automatically deploy patches, reconfigure security policies, and re-route traffic to harden its defenses against anticipated attacks. This would create a resilient, self-healing security posture that can evolve and adapt in real-time, just as threats do. While full autonomy remains a forward-looking goal, the current market trend toward deeply integrated, data-centric platforms with extensive automation capabilities represents a clear and determined step in this direction, promising a future where our digital infrastructure can largely defend itself.
Explore More Like This in Our Reports: